500IT Cryptography Assignment Sample
IMPLEMENTATION OF CRYPTOGRAPHY IN ZAMBESI RETAIL BUSINESS
Introduction
Cryptography has helped to maintain the privacy side of data and information of any kind of organization. Nowadays it is very natural that organizations promote the products and brands online or even through websites and here is the main problem. The online application has provoked cybercriminals to hack, destroy, and steal information and use it illegally. Zambesi, a UK-based company, has led a promotional advertisement through the website of the company, and in this process how cryptography helped will be discussed in the project.
UML sequence diagram system
A sequence diagram is a part of an interaction diagram that helps to describe in which order and how the objective works of a group have to be done. Business professionals and Software developers are using this sequence diagram for a better understanding of the requirements of a new system and existing process. UML or Unified Modeling Language, a modeling toolkit, guides the notation and creation of various types of diagrams. There are two types of sequence diagrams like UML sequence diagrams and code-based diagrams but this project for a retail business named Zambesi implemented UML diagrams for its security procedure.
The benefits of using sequence diagrams can be explained from many aspects like this procedure presents a sophisticated model procedure with a proper explanation and logic about the operation or functions. This procedure also looked after the interaction process of the components and objects if the work is completed or not. This diagram is also helpful in planning and understanding the functionality in detail and it can be existing as well.

Figure 1: UML sequence diagram system
(Source: Campean and Yildirim, 2017)
UML sequence diagram is very helpful for a retail business as it shows the relation in the object of billing counter, customer stock, store, and other parts. Campean and Yildirim, (2017) mentioned that by applying this diagram in the retail management business the admin is provided the opportunity to login from with credentials and after completing the login process it is easy for the admin to manage the overall operation which is going on in the other parts. Applying this above process, the business named Zambesi works efficiently and secures its data from cybercrime criminals.
Concept of Cryptography
The main concept of Cryptography revolves around the phrase of security output in an organization. The involvement of Cryptography has countered the problems related to privacy, security, and keeping safe the information when transferring which arises several advantages and disadvantages in the process.
Advantages
Zambesi has invested a huge amount of money in the court of IT technologies for the sake of security and to examine future strategies which can be included. The information kept in a safe place from the employees and the hackers and in this process, cryptography brings various advantages like:
- Large-sized businesses needed the involvement of cryptography mostly because a big file required a secure method of transfer otherwise it could clash. In a large-sized business, it is very obvious that the company has to assess large-sized information in the state or even outside the state. Perimeter security solution methods do not provide the organization that opportunity, but cryptography fulfills the requirements. Almuhammadi and Al-Shaaby, (2017) stated that if an industry has the necessity of complete data security and protection, cryptography is the solution. For that advancement, Zambesi has included this strategy in the business process.
- The use of smartphones is very much obvious in the present time and for that many people sign into the system with personal information from various devices due to which the problems occur. At that time cryptography has included software that gives data encryption that eased cybercrime. Potential thieves have continuously tried to steal information for bad use. Security provided across various devices by Cryptography is a major advantage that is highly appreciated.
- A major advantage of cryptography is maintaining integrity. The cybers thief has alternated the main information with wrong information for the safety of legal exhaustion because most of the time after stealing information, industries could not have any idea about the loss.
Disadvantages
- Cryptography initially has no disadvantages for usage but in crucial times in which the users are in hurry, it is very hard to assess the process. The information is locked in a secure store with several passwords and encryption processes. In the period of decision making, it is important to find all the information in hand at that time, but cryptography has done the same. According to Karolin et al. (2018), this factor made the security process somehow difficult which brought disadvantages for the organization.
- Organizations have used cryptography initially, but it has some limitations as well. For that reason, if the organizations only depend on cryptography is not right. With cryptography, it is needed that other processes have to be implemented.
Theory of Cryptography
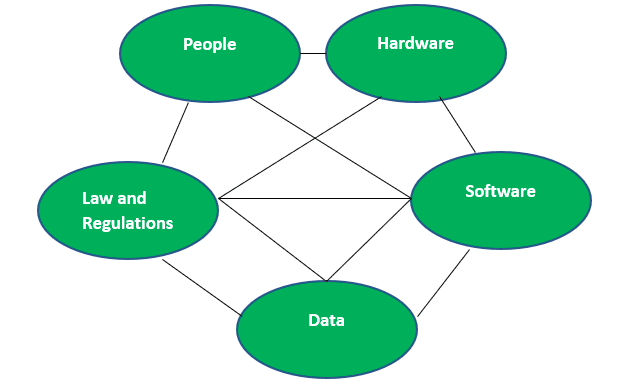
Figure 2: Security-technical system theory
(Source: Sadok et al. 2020)
Security-technical system theory has been related with Cryptography as in the theory the organizations mainly focused on the privacy, protection, and security of data and information from any disturbance. In cryptography, the same topic has been enlightened. Security can be held if IT technologies can be included in the system. Cryptography is also a process that promotes technologies for better results and the storing of data and information in a safe place. Sadok et al. (2020) mentioned that it is obvious that technologies have been used in this and better adaptation of technologies seems to be very meaningful for the organization. Zambesi has also included this theory for the process of cryptography. Being a retail industry Zambesi has a huge amount of information for transfer and gathering which needs an effective technical efficiency and the theory provided the same.
Modeling tools of Cryptography
Bell-LaPadula Model can be applied as a modeling tool of cryptography because it gives a mathematical overview of the security policy. According to Kommuri, (2019) the Bell-LaPadula Model has some distinct properties that are simple security property, security property, Strong Tranquility Property, and Weak Tranquility Property.
The Biba model is also applicable in the cryptography process because it focuses on the integrity of the organization. Zambesi needs proper integrity in the information otherwise it is very difficult to make the activities of the organization perfect. Organizations ensure that high scale security must be logged in the information security settings and the model has also supported it. Integrity Axiom and simple Integrity Axiom are the core classes of the Biba model.
Cryptography is a process that provides proper guidance in information security and Bell-LaPadula Model, Biba model both have support and encourage the system in the organization. According to Oshogbunu et al. (2021), Simple Integrity Axiom has provided a security assessment of the information security from top to bottom for which the organization can trace the faults and work according to it. Integrity Axiom also helps to control the security at a high level and for this reason, it has not been taken as mitigation of information security assessment.
The predicate and Propositional logic cryptography
This predicate and Propositional logic are used in the field of mathematics and computer science to get the conclusion about the result if it is relevant or not. The predicates are mainly the characteristics and some additional information that are used for the better expression of the subject. A predicate that is qualified properly is a proposition that can be used for the prediction of the other variables. According to Wehmeier, (2018) this logic is used in the retail business to predict the further revenue of the business so that the company can move according to the plans and make success. The propositional, is a declarative character of a sentence, has a truth value. It is used to identify the truthiness of any sentence. Granmo, (2018) mentioned that this is used in the retail business to recheck the data or the information and search for the truth about the data which are collected. It also looks for the security of the collected data and stores it securely.
Evaluation of Hashing and Cryptography method
Cryptography has several stages on the way to secure the information of an organization, Hashing method is one of the existing methods. Application for Digital signature has been done by the Hash system and to resist the fraud in that process cryptography hires hash function. The digital process of the signature has needed encryption otherwise without delay it can be duplicated and create complexity in the business (Luo et al. 2020).
Conclusion
In this report, the discussed topic is cryptography which carries a huge investment in every organization. An effective technique that can resist such cybercrime is Cryptography because by encryption process all the message and important information has been secured at a locked store which cannot be hacked or destroyed. Zambesi has invested a large amount in the security of information. The cryptography process has some advantages and disadvantages because it is a matter of implementing technologies. The report has also discussed the theory that suits cryptography and the theory of security technical systems. Some models discussed in the report are the Biba model and Bell-LaPadula Model. The evolution of Hash is also applied in the report to support the discussion. All the topics are related to supporting Cryptography.
Reference list
Almuhammadi, S. and Al-Shaaby, A., 2017. A survey on recent approaches combining cryptography and steganography. Computer Science Information Technology (CS IT).
Campean, F. and Yildirim, U., 2017. Enhanced sequence diagram for function modelling of complex systems. Procedia Cirp, 60, pp.273-278.
Granmo, O.C., 2018. The Tsetlin machine-a game theoretic bandit driven approach to optimal pattern recognition with propositional logic. arXiv preprint arXiv:1804.01508.
Karolin, M., Meyyappan, T. and Thamarai, S.M., 2018. Encryption and decryption of color images using visual cryptography. Int. J. Pure Appl. Math, 118, pp.277-281.
Kommuri, S.T.R., 2019. Building Security Aware E-Commerce Web Applications.
Luo, X., Chen, C., Zhong, H., Zhang, H., Deng, M., Huang, J. and Hua, X., 2020. A survey on deep hashing methods. arXiv preprint arXiv:2003.03369.
Oshogbunu, M.A., Vajjhala, N.R., Rakshit, S. and Longe, O., 2021. Applying natural language processing algorithm for predicting consumer product preferences in retail stores. Available at SSRN 3833695.
Sadok, M., Alter, S. and Bednar, P., 2020. It is not my job: exploring the disconnect between corporate security policies and actual security practices in SMEs. Information & Computer Security.
Wehmeier, K.F., 2018. The proper treatment of variables in predicate logic. Linguistics and Philosophy, 41(2), pp.209-249.
………………………………………………………………………………………………………………………..
Know more about UniqueSubmission’s other writing services:

