CN7026 Cloud Computing Assignment Sample
HERE IS SAMPLE OF CN7026 Cloud Computing Assignment
INTRODUCTION
In the network system and the administration, the Cloud service providers plays a pivotal role. With the computer technology development, the virtual machine has become one of the highly researched topic. These cloud service providers are said to be as the companies which provides the services of network, business applications and infrastructure based on the cloud platform. These services of cloud is installed and is hosted in the network data enters and it can be accessed easily by the individuals or the companies with the connectivity of the network.
The biggest advantage of the cloud service provider is that its economies of scale and its efficiencies. Other than building the own infrastructure by the companies or the individuals for supporting the applications and the internal services, these services can be buy directly from the cloud service providers which offers many customers the services within a shared infrastructure(SDx, 2015)
The various types or forms of the services that is provided in the platform of cloud by the cloud service provider along with the software, and is known as the software as a service, the next one is the platform as a service, which develops and compute a platform in order to develop the applications for hosting, and third one is the infrastructure as a service, in which it computes the whole infrastructure of the network.
Some of the examples of the cloud service providers includes, the Rack space in which it is developed as a company for web hosting and can buy IAAS or PAAS. The cloud providers focus mainly on the particular verticals, like the healthcare hosting applications in order to secure the IAAS environment(D. Gupta, 2006).
PROJECT PLAN
In the current trend, the technology for virtualization, the technology of migration, security technology, cloud service providers, and the load balancers are the main technologies is likely to be used. The usage of the virtual machines buy the computer can be segregate all the resources of data, and the resources of software, and the hardware resources.
These technique of virtualization helps to separate the software and the hardware management and offers the performance isolation features. The project plan mainly focuses on the current tools and the methodologies used by the cloud service provider for the security purpose.
CLOUD ARCHITECTURE
In the cloud computing technology, the virtual machine is said to be as the computer emulation system. These virtual machines mainly depends on the architectures of the computer and offers the physical computer functionality. The implementation of the virtual machines may include the software or the hardware or the combination of both(Wapqing Li, 2010). The virtual machines are of two types namely,
- System virtual machines
- Process virtual machines
The system virtual machine offers the required functionality for executing the whole operating system. A native execution is used by the hypervisor users for sharing the hardware and managing it. These system virtual machines allows the multiple or many environments to be isolated and differentiated from each other but on the same machine.
The process virtual machines are developed for the execution of the computer programs in an independent platform environment. Some VMs are allowed for the software application executions, and also allows the computer resources to be split.
The loud architecture is classified as:
- Front end
- Back end
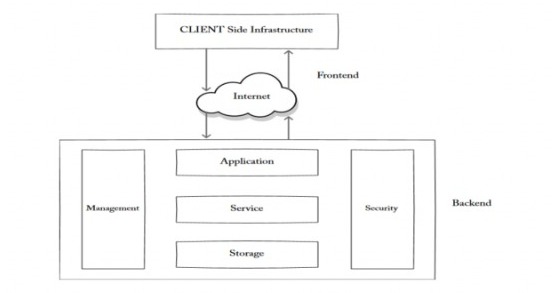
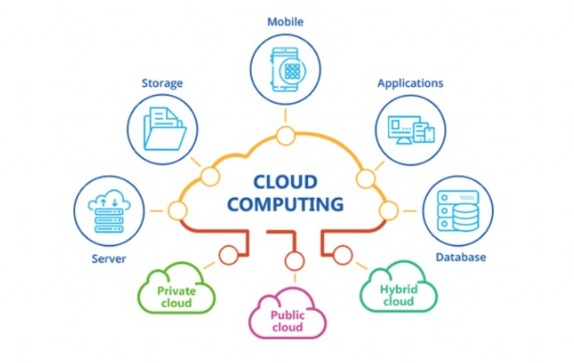
Fig 1: cloud service provider Architecture
These virtual machines of the cloud service providers helps the users to do the operations like copy, create, save, modify, and to read the text in a file.
CLOUD PLATFORM
The cloud service providers are of three types namely,
· Platform as a service
· Software as a service
· Infrastructure as a service
The platform of cloud by the cloud service provider along with the software and the necessary programs, and is known as the software as a service, the next one is the platform as a service, which develops and compute a function on the platform in order to develop the applications for hosting, and third one is the infrastructure as a service, in which it computes the whole infrastructure of the network.
VIRTUAL MACHINE CONNECTION
The virtual machine connection is done based on the architectural process and along with the techniques of migration. These migration techniques are implemented. For the implementation Xen method is used. Xen is said to be as the x86 machine virtual monitor.
This monitor machine of virtualization, is simply allows the operating system to share the hardware in a secure and save managing resources. The VMM also called Xen hypervisor is allowed for the direct accessing of the hardware, with the domains of the Xen, in which the virtual machines are run as the guest in the OS instances. This method uses the receiver or the send model depending on the transfer state capabilities in the virtual machines which is implemented as the two sided interface.
The novel based system of the virtual machine and its connection is said to be as the transparent method of migration along with its applications. Each process is virtualized and view in various operating systems like the address of the networks. We can do a decoupling process from the dependencies of the host in which the migration units are formed(A. Menon, 2005).
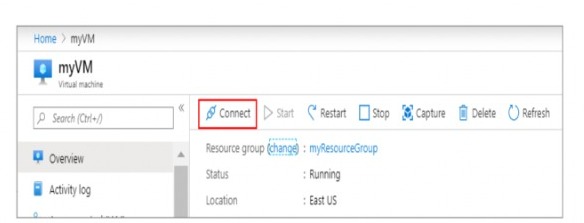
Fig 2: VM connection(C. Clark, 2005).
DATA CENTER AND STANDARDS
LOAD BALANCER
A devices of the load balancing which acts as the proxy reverse and the network is distributed which offers the server traffic of the servers. And theses load balancers are help in order to maximize the capacity based on the concurrent network users. These load balancers are fully helped for the application of the performance of the overall networks along with the network sessions, and the application of the maintenance.
The requests are depended on the protocols of the application layers like the hyper-text transfer protocols. This method receives the request load balancing types in order to distribute the configuration of the server algorithm.
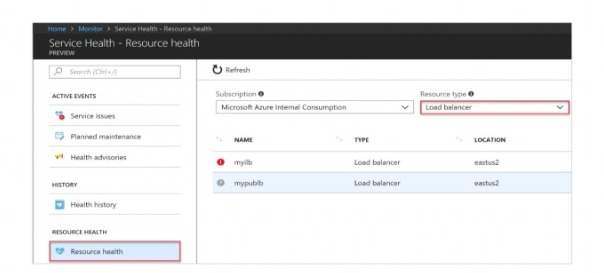
Fig 3: Load Balancing
AUTO SCALLING
The automatic scaling is a technique used in the cloud platform and the resources in the server and is measured based on the server numbers and it varies based on the load of the machine. In the companies the servers load will be typically low. The computing capacity mainly runs on the less type sensitive and we should pay for it.
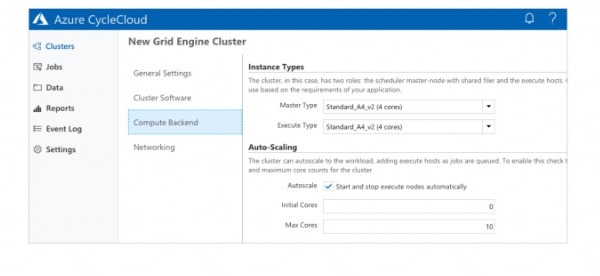
Fig 4: Auto scaling
IMPLEMENTATION USING AZSURE CLOUD PLATFORM
The Azure is said to be as the cloud service computing and is developed by the Microsoft mainly for the purpose of testing, managing, deploying, and building the services and the applications. In the virtual machines, the applications and the services mainly allows its users to configure its images on the machines based on the azure.
In Azure, most of the users run Linux, based on the azure sphere. It is said to be as the public platform of cloud computing and offers the range of services of cloud including storage, analytics, networking and computing. Users have the allowance of choosing the required services from the cloud and they can develop applications newly, or even they have the rights for running the applications existing in the public cloud(Stephen Bigelow, 2016).
The platform of azure helps for the managing of the challenges in business, in order to meet the goals of organizations. This service offers the user for the usage of technologies and tools flexibility. The subscribers of these services are mainly help to create the virtual machine resources and data base.
In the above diagram, the Ubuntu is used for attempting the network, and to check how the virtual machines are checked monitored and run, and the access of the Ubuntu is used based on the drivers and hardware.
The cloud service providers mainly offers the services like the software, platform and the infrastructure services for the data communications.
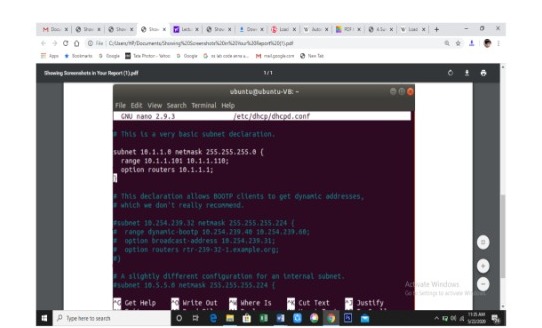
The Ubuntu software is mainly used in the configuration of the settings based on the client server subnet and each subnet has the routers individually as the gateway or the path for the communication platforms.
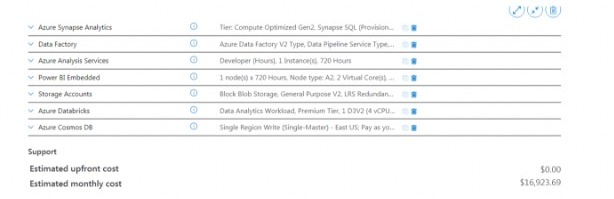
MICROSOFT AZURE CLOUD PRICING
Following is the pricing of using Microsoft azure cloud service for the given project
ANALYSIS AND REFLECTION
In this study we have seen in detail about the cloud service providers like the software as a service, platform as a service, and infrastructure of service. These service providers offers the network service to the users and allow them to save the data in the cloud platform.
CONCLUSION
This research is mainly based on the technologies currently presented in the system of virtual machine. In the virtual machine, the resource technology for scheduling is used, with the technology of the performance evaluation. In the future, the virtual machine and its system presents the architecture of the CPU, the mode of management and the system resources along with the valuation of the performance in the virtual machine system in multiple systems.
REFERENCES
1.A. Menon, J. R. (2005). Diagnosing Performance Overheads in the Xen Virtual Machine Environment. Proceedings of the 1st International Conference on Virtual Execution Environments , 1-10.
- C. Clark, K. F. (2005). Live Migration of Virtual Machine. Proceedings of the 2nd Symposium Networked Systems Design and Implementation, 1-15.
- D. A. Menasc´e, “Virtualization: Concepts, Applications, and Performance Modeling”, Proc. 31th Int. Computer Measurement Group Conf, 2005, pp.407–414,
- D. Gupta, L. C. (2006). Enforcing Performance Isolation across Virtual Machines in Xen. In Proceedings of the 7th International Middleware Conference, 342-362.
- R. Sailer, T. Jaeger, E. Valdez, R. Caceres, R. Perez, S. Berger, J. L. Griffin, L. Doorn, “Building a Mac-based Security Architecture for the Xen Open-source Hypervisor”. Proceeding of the 2005 Annual Computer Security Applications Conference, Dec. 2005, pp. 276–285, doi: 10.1109/CSAC.2005.13
- SDx. (2015, MAY 20). What are Cloud Service Providers?Retrieved from SDXCENTAL: https://www.sdxcentral.com/cloud/definitions/what-are-cloud-service-providers/
- Stephen Bigelow, M. R. (2016). Microsoft Azure. Retrieved from searchcloudcomputing: https://searchcloudcomputing.techtarget.com/definition/Windows-Azure
- Garfunkel, M. Rosenblum, “A Virtual Machine Introspection Based Architecture for Intrusion Detection”. Proceedings of the Network and Distributed System Security Symposium (NDSS),2003.
- Wapqing Li, Y. L. (2010). A Survey of Virtual Machine System: Current Technology and Future Trends. International journal of computer applications, 1-6.
24/7 Chat Support | Get A+ Grade | Written by Top-Notch Subject Experts | 20% Off 1st Order |
Know more about UniqueSubmission’s other writing services:

