CYBER DEFENCE
The assignment is considered with the open source intelligent framework to collect the source of the information for making the threat model related to the defined scenario.
Then based on the threat model the intelligence and vulnerability is has to analyse based on the scenario. The threat model can design using the open web application security project (OWASP) and the sources are gathered from the NIST vulnerability databases.
The necessary process is followed in this assignment to analyse the different kind of information for creating the threat model and the various key threats are identified in the selected scenario and then presented the risk table along with the measurement of the low, high and medium level of impact occur with the threat process.
Then analyse the threat impact in the business like business failure and any interruption happen in business. It suggested the mitigation actions for the measured threats and to reduce the impact of the threat. Based on the above analyse the information security action plan is created to measure the various vulnerability and reduce the threat of the organization.
The contingency measure is also done with the various analyses of the processes. Like that the scenario is considered with threat creation and maintain for the various results.
Overview of the intelligence sources
The source information is gathered from the www.ncsc.gov.ukand NIST vulnerability data base to relate the considered scenario along to the incident happened. The scenario is consider in this process is MoneyTransfer4U organisation that is done the money services across the UK high street.
It has the stores across the UK and this is connected through the metropolitan area network the daily transaction is done with the FTP of the head quarter to the each of the other stores. This organisation is used the MySQL database for maintaining the money transfer information and the customer details.
The transaction can be done through the staff available in the store or the customer can create the account and log in along with the information maintenance of the customer details and bank account details etc.
there is no verification service during the transaction process the offset service will be enable it will send the information to the email for the verification process to analyse it then transfer the money. In this process the some of the staff are working in home also they created password for their accessing process there is no organization policy is followed for the communication process.
So there may the threat XSS will happen that is cross site flaws will happen under the estimation of the various analysis this may lead with the process of the evaluation.
The sources is consider with the process is CVE 2007 – 5201 is consider with the FTP backend for duplicity process. That is sendingthe password as the command line argument then it is allow the local user to access the password for the various purposes.
This source has the medium vulnerability level with various measurements and it find the bugs related to the user security related to the password creation so that it is choose as the resources for this Moneytranser4U organisation.
The ncftpput measure the FTP user file and the FTP pass file for the threat prediction process. So that it is directly related to our selected scenario and it is utilized in the process. The duplicate create with the ftpbackend that is related to the FTP password vulnerability.
In this each class is design with the error packet measurement and it is created with the issue of the duplicity creation of while creating the password or using the password. The attacker can exploit the issue for obtaining the password that is used in the FTP connections.
This will be exploiting with the standard tool that is done by the attacker then it is transferred to the FTP connection establishment process. This attack is related to the selected scenario of the organisation Moneytransfer4U for obtaining the solution for security process.
This is analysed with the creation of the threat and analyse with the different kind of key factors involved in the vulnerability. This vulnerability is measured with the mitigations and exploit with the solution for the threat process. The information security action plan is deployed based on the threat identified in the above analysis.
The threat modelling is the structure that is contains the information of the activity for identifying the object based threat and managing the object based threat. The threat modelling is the essential step for the application to analysis the architectural risk.
Without of the threat modelling process the security is the question mark of applications. It is the process to analyse which threat is identified and prioritized for the various communication process.
Then it is also provide the systematic analysis of the attacker’s information and mostly used the attacker vectors range then which is the most desired attacker involve in the application like that all the information is gathered through the thread model creation and execution.
The identification of the thread and what are the mitigations are available related to the threat and how it is validate through the various tools or techniques for the application security process. The validation process is predicted if any attacker is undergone with unnoticed process.
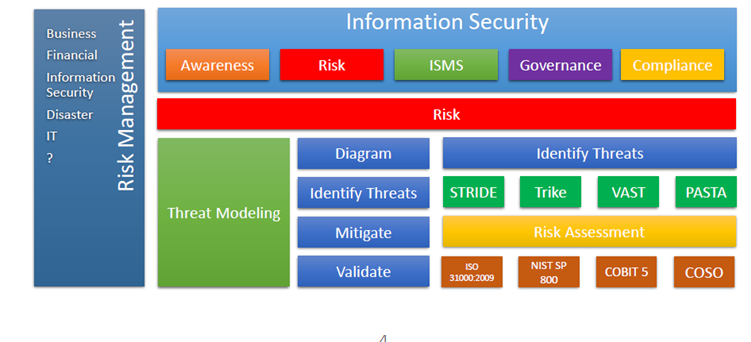
The information security process is considered with the awareness, ISMS, governance, compliance and risk. These are the analysis of the business financial information security process related to the various functionality processes. Based on the above diagram the threat modelling is evaluated with the diagram representation and identification of the threat and the mitigation process, validate process.
The diagram representation is done with the help of OWASP. Before design the model have to analyse the possible vulnerability will occur and based on the analysis the threat model will design. The sources are used for the analysis and design the treat model for the Moneytransfer4U organisation.
Building the threat model is considered with the program manager of the overall process involved in the organisation that is owner is the responsible for the full process. Then the tester analyse the threat in analyse phase then using the threat design to drive the test plan. Then it is customized with the various factors influence in the process along to the communication process.
The level 0 of threat model is design with the basic structure involved in the organisation Moneytransfer4u. The main process involve in the organisation is transfer the money depends on the customer need that is done by the employee of the store or the customer itself through registration with the customer profile information and bank information, address information.
The organisation is consider with the many store across the UK so while designing the threat model concentrate on the multi store and the customer is maintained with the multi store then money transfer process will happen in many store simultaneously.
The password creation is not done with organisation policy so the attack can hack the information of password easily related to customer or the employee of the store. All this situation is analysed while designing the threat model of the organisation and provide the architecture with the following manner.
Level 0 Threat Design
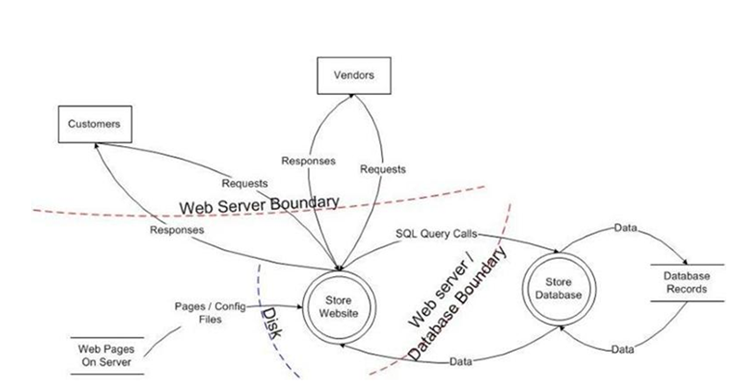
The above diagram is representing with the store website along to the various stores. There are various store are has the own database for the communication and maintain the vulnerability of the various process communication.
The various web pages are involved in the communication the customers and vendors are consider the action persons. The customer provide the request to the store for accessing the webpage then the store reply to the customer for the accessing the information of the customer.
The web pages on the server can pass the configuration files to the store website then it is calculated with the various performance measurements. The request and response ishandling with in the process along with the web server. The processing is considering with the database records along to the communication process.
The level 1 is consider with the next stage of the analysis process of the organisation consider with the server boundary. The customer is analysed with the authentication transfer that is evaluated with the user belongs to the applications. The authorization is measured and validate with the correct account type or the policies involved with the organization is encountered.
In this analysis if the customer is want to transfer the amount from their account means first it is need to withdraw of amount form their account to store account then it is transfer to the corresponding account. In this time the customer can log in using the user name and password of their own account information.
The password setting is not followed the any rules so the attacker easily access the information of the user name and password. And these information is gathered through the denial of service attack and XSS attack that is cross sites scripting flaw that is need to evaluate the various performance measured by the attacking process.
If the bad account is encountered means that is deal with the bad account number then it is deal with the security evaluation process. The security evaluation is done with the boundary setting value while transmitting the information through the file transfer protocol.
Level 1 Thread Model
The transaction will perform under the audit log process it is check the conditions of the authorization and also it is deal account balance and new balance process. Identify the process involve in the withdrawal request and also it is made with effective communication line process.
The trusted boundaries are instructed in the threat model. The vulnerability is consider with the various analysis made in the account details and reading the username and password from the customer or employer if the store. The boundary value is maintained with the necessary input value that is mapped with the other kind input given by the attacker.
Like that all the measurement is done for creating the threat model related to the Moneytransfer4U organisation. The threat model is designed with the analysed vulnerabilities related to the scenario and made analysis based on the data flow from the one point to the other point of the transaction process.
The boundaries are considered with the machine boundaries, integrity boundaries and privileges boundaries. The process is taking with the channel for communications here consider the FTP then it is monitor with the required analysis.
The threats can happen in unnoticed situation that is needed to monitor by the task to overcome the threats in the various situations. Based on the application it is consider for measurement and it is analysed through the risk factor involve in the each threat process.
Threats by the application vulnerability
Here analyse the vulnerabilities with the application and how can it is monitored and mapped into the various level of process according to the necessary communication. Type
| S.no | Types of vulnerability | Explanation |
| 1 | Input Validation | It is done with the buffer overflows and the cross site scripting is evaluating (XSS) , the SQL injection process |
| 2 | Authentication | The cookie attack, brute force attack and the cookie replay done the credential theft process, the network crossing process. |
| 3 | Authorization | The privilege of the security analysis method, luring attack, disclosure of the confidential information. |
| 4 | Configuration process | Monitoring the un authorized access of the account, the gather the information of the configuration data, the lacking of the service account and the privileged process to leak the individual information |
| 5 | Sensitive information | The data tempering and the access of the sensitive data is maintained with the storage process. |
| 6 | Managing the session | The session hijacking is maintained in the middle portion and it is consider evaluating with various analyses. |
| 7 | Cryptography | The key management is the process of maintaining the information with secure manner so it is look poor, weak encryption process. |
| 8 | Manipulation of the parameter | The manipulation happen along with the query, HTTP header, forms field and cookie manipulation also. |
| 9 | Managing the exception | The denial service is deal with the process measurement along with the exception management system |
| 10 | Auditing and logging process | Sometimes the attacker exploit the information without any tracing process and the user can deny the services of various operations. |
SQL injection
The thread will be analysed with various level measurement is done with the applications which is related to the input and output of the process. The attack can happen based on two categories that is web based attack and system based attack.
During the usage of the virtual platform the web based attack is easily occur and the system based attack is happen in the scenario of the system based applications. The web based attack is happen with the website based process. SQL injection attack can occur to inject the some of the information display in the website and then it is translate into the required information related to the confidential information.
Phishing
This attack can occur and steal the information related to the sensitive data that is user name and password, credit card details like that. It will happen during the untrusted electronic communication related to the necessary action. This may be attack the credential information of the various process related to the customer profiles. The electronic communication is happen in between the process and also it is communicate with the one user to system.
Denial of service
The network sources are unavailable while communicate the information from one customer tot eh next analysis process. This is also analyse with the various processing of traffic can occur and that will be affect the packet information along to the require communications. It is basically use the single system or the single internet layer for the attacking the system.
It can be classified into the volume based one, protocol based attack and the application layer based attack. The saturate bandwidth is consider for the volume based attack and server resources and packet information is maintained with the protocol attacks then crash the web server is maintained and measure the request per second is done with the process.
The attack is measured with the input and output basis process. Here consider the input vector for the analysis process and then it is deal with the various analyses.
The input vector is measure with the input type here consider the first URL query strings that is measure the query string parameters from the URL and the support of the Protocol utilization. Then consider with the regular form filed this is enabling and passing the information to the forms that is related to the services and it is measured with the HTML.
The parsing information from the hidden fields is considered with the various analyses. This may deal with the Dynamic HTML pages that are request from the servers and it is enabling with the input recommendation of the application then it is deal with the secure transaction process.
The HTTP request is communicate between server and client using the hypertext transfer protocol. In this the process is consider with the each store that is running separately and one store act as the head office of the organisation that is Moneytransfer4U.
The head store access the information of the all other store information that customer details and money transfer details. In this the tread may happen during the money transformation of the customer through the store staff. Here the password of the staff is not generated by organisation rules that may be change according to the usage of the system information.
The output vector is considered with the HTML pages and the HTML responses of the server page. This will be analysed with the different categories of the process related to the environment. The possibility of thread is analysed with the various key factors along to the application scenario.
Threats Analysis with mitigation techniques
Threat Type I
In this type the thread is analysed related to the key factor of various input process of applications.
The type of the threat is occur during the transaction process of customer is SQL injection it is basically under the category of the input validation process and the mitigation techniques is consider for this type of threat is to validate the user input, using the parameterized procedure for storing the value instead using the SQL maps.
The SQL maps are very dangerous process for storing the information of the customer. Then the mitigation can chose for the process is analysed with the iBatis SQL Maps and the data access objects. The risk factor of this thread is considered with the high level process and the effects of graphs will be analysed through the data integrity and loss of confidentiality of the data.
Threat Type 2
Now consider the threat analysis based on the cross site mapping process. If the customer wants to transfer from the one account means they want to register their personal information in the website along with the bank, address details. Otherwise they request to the store staff for transfer the money the staff can log in with their details then transfer the amount.
During this process they have to access the more than site at the time the attacker may use the cross site scripting process then gathered information of the customer profiles and account details or the staff information of the particular store.
This is cross site scripting (XSS) it is based on the input type that is given by the user and the mitigation is consider with the HTML encode and URL decode methods for the validation and also consider the string for the value measurement process.
The execution process is consider with the various analysis involve in the process that may be related to the final transformation process.
Threat Type 3
The threat is analysed with the canonicalization that is the process is executed with the same coding and the limitations is consider with the set of configuration file this may lead to analyse the difficult measurement for the execution process.
The request for encoding and response for the encoding process is considered and this may be handle with the mitigation techniques of the web configuration file that is belongs to the communication. The decision process is considered with the store value along to the input based analysis. The access to privileged resources are considered and then it is implemented escalation of the privilege and the risk is in the moderate level for the accessing the threat.
Threat Type 4
This key factor is analysed with the sensitive information and this will be evaluate with the various process of authorization. The threat is disclosure of the sensitive data that is confidential data. It is come under the category of the authorization.
The mitigation techniques are consider for this type of the process is create the function that is check the sensitive data before it execution. Here before the transaction happen the user can check with the sensitive data that is related to the account type and personal information. Then it is involve with the transaction process check with the necessary conditions.
The mitigation process is support to encrypt the customer password and other personal information, account information of the customer. So it will be maintain with the secure manner. The risk level is considered with the high for accessing and measuring the information of the user.
Information Security Action Plan
The information security is consider with the various analysis based on the evolution of certain process that may differ category by category levels.
The above shows the information of the action plan of the moneytrnasfer4U organisation that is consider with the various analysis of process. In this using the various types of the threat analysis we have to first identify the problem related to the applications this may be change according to the user. Then the identified problem is analysed with the various problem related to that then it is directly related to the tree analysis format.
Then identify the attack related to the purpose of the attacker and how it is related to the various issue this may be analysed with the different category of the process. In this each task is mapped with the mitigation level then it related to the requirement analysis of the process.
Then based on the analysed problem analyse the solution using the mitigation techniques related to the threat which is web based or system based problem. Then check with the priority issues that are mapped with the various analysis of the privilege taken by the customer or the employee of the organisation.
If the money is transferring process is analysed clearly to avoid the hacking problem with the efficient of the action plan. Then planning the actions regarding to the persons that is customer or the store related to issues like that it is generally measures the problem along with the necessary action this may deal with the process of managed situation.
Then it is analysed with the various resources and that may be deal with the different kind of factors communication to each of the store and manipulated with the necessary communication. Finally use the solution to implementation with certain scenario and predict the necessary solution to the various factors related to that problem.
The action plan also consider with the scenario of the process. The information related to the sensitive data that is user name and password, credit card details like that. It will happen during the untrusted electronic communication related to the necessary action.
This may be attack the credential information of the various process related to the customer profiles. The electronic communication is happen in between the process and also it is communicate with the one user to system. Based on this the action plan carryout the problem and execute with the necessary conditions. The following threat type is also considered with the action based on the analysis it is explained well manner.
Threat Type 5
This type of threat is considered with the unauthorized access to configuration of the store. The attacker can analyse the possibility of the unauthorized access mode and also it is maintain with the necessary mode.
The configuration process is need to effectively for avoiding the un authorized person usage that is done with the mitigation techniques related to the various type of analysis carried out the process along to the medium levels.
The configuration file is maintained with the outside of the web space and also it is deal with the necessary input and output. The privilege of the access process is considered with the measurement and also it is directly related with the command injection process. The risk factor of this threat is relative with the high level and it is maintained with the web logs.
Threat Type 6
This threat is treated with the crass the app server. Here the Moneytransfer4U organisation is consider with the many number store across the country so it is evaluated with the various store data bases. The all the data base is connect with the head office data base that is created and maintained with the MySQL data base.
The denial of service is happen along with the attackers can able to trash the organisation server it is comes under the category of the exception management. So the mitigation techniques are need to follow for this kind of threat is to handle the exceptions properly and it is redirected into the proper channel.
The risk management is in medium level it is always measured with respective server of the operations. Like that the thread will be identified with the various key factors and also it is maintained with the respective analysis of the process.
Threat Type 7
This is analysed with the exception management system in this the threat will be analysed with the information disclosure of the process and this will deal with the various attacks can happen through the employee of the organisation.
The Moneytransfer4U is considering with many stores and the money transfer process can do in every store by the different kind of the staff. So sometimes the staff can handle the sensitive information very openly then it is easily identify the attacker and used it then find the information related to the other store also.
This is done with the cross page recognition and measured with the various analysis of the process. The mitigation techniques is used for this analysis is consider with avoid the raw exception output to the user. This may lead with the necessary communication process related to the facilities of attack and the information disclosure process.
Threat Type 8
It is basically handle the manipulation process. The manipulation happen along with the query, HTTP header, forms field and cookie manipulation also. Sometimes the attacker exploit the information without any tracing process and the user can deny the services of various operations.
It is executed under the parameter manipulation and the mitigation techniques used for this scenario of the organisation is to validate the input is very important process because through the input the attacker can hack the information very easily.
so the user input is not trusted that is encrypt for every query strings and this is done with the use of the Post not get value and if the information is having the sensitive data means this will handle the encrypted session do not use the query strings for the this type of handling process.
So that the data is maintained with secure manner and that will be react with the various analysis process. The architecture is used for this process is related to the problem that is usual of the J2EE application. The risk factor of this thread is considered with the high level process and the effects of graphs will be analysed through the data integrity and loss of confidentiality of the data.
Thread Type 9
The command injection id very high level risk that is done with the input category of the process this may be lead with the problem introduced by the other experimental process. Here the store is link with the various processes along with individual and the head store.
So the URL strings are invoked with the various actions for the user. If the user is not authorized means this type of the inject arbitrary is clearly validate and executed.
It is based on the mitigation of choosing the MVC architecture related to the effective communication process. This is considered with the very bad problem that need to compromise of the whole system along with the execution of the arbitrary commands executed while communicating the various store through the head store for the money transferring process.
Like that various applications are used for the threat analysis and the mitigation process of the every product.
The above analysis is done with the systematic understanding and critical analysis cyber defence, network attacker analysis for the various process involved in the moneytransfer4U organisation. The threat model can designed using the open web application security project and the sources are gathered from the NIST vulnerability databases.
The necessary process is followed in this assignment to analyse the different kind of information for creating the threat model and the various key threats are identified in the selected scenario and then presented the risk table along with the measurement of the low, high and medium level of impact occur with the threat process.
Then analyse the threat impact in the business like business failure and any interruption happen in business and the information security action plan created for the efficient execution of the process.
- Brændeland G ,Refsdal A ,Stølen K . Modular analysis and modelling of risk scenarios with dependencies. J Syst Softw 2015;83(10):1995–2013 .
- Chen X ,Liu Y ,Yi J . A security evaluation framework based on STRIDE model for software in networks. Int J Adv.Compute Technol 2014;4(13):269–78 .
- Li X ,He K ,Feng Z ,Xu G . Unified threat model for analyzing and evaluating software threats. SecureCommon Netw 2016;7(10):1454–66 .
- Li X ,Liu R ,Feng Z ,He K . Threat modeling-oriented attack path evaluating algorithm. Trans Tianjin Univ 2017;15(3):162–7 .
- Liu X ,Zhu P ,Zhang Y ,Chen K . A collaborative intrusion detection mechanism against false data injection attack in advanced metering infrastructure. IEEE Trans Smart Grid 2015;6(5):2435–43 .
- Magklaras G ,Furnell S ,Brooke P . Towards an insider threat prediction specification language. Inf Manag Comput Secur 2016;14(4):361–81 .
- Hydara I ,Sultan AB ,Zulzalil H ,Admodisastro N . Current state of research on cross-site scripting (XSS) –a systematic literature review. Inf Softw Technol 2015;58:170–86 .
- Idziorek J ,Tannian M . Security analysis of public cloud computing. Intl J Commun Netw Distrib Syst 2012;9(1/2):4–20
- Lagerström R ,Baldwin C ,Maccormack A ,Dreyfus D . Visualizing and measuring enterprise architecture: an exploratory BioPharma case. In: Proceedings of the 6th IFIP WG 8.1 working conference on the practice of enterprise modeling (PoEM); 2013. p. 9–23 .
- Katsikeas S ,Johnson P ,Hacks S ,Lagerström R . Probabilistic modeling and simulation of vehicular cyber-attacks: an application of the meta attack language. In: Proceedings of the 5th international conference on information systems security and privacy (ICISSP); 2019. p. 1–8 Feb .
- Lagerström R ,Johnson P ,Ekstedt M . Automatic design of secure enterprise architecture: work in progress paper. In: Proceedings of the trends in enterprise architecture research (TEAR) workshop, in conjunction with the IEEE EDOC conference; 2017. p. 65–70 .
- Latif R ,Abbas H ,Assar S ,Ali Q . Cloud Computing risk assessment: a systematic literature review. Future information technology. Lecture Notes in Electrical Engineering, 276. Berlin, Heidelberg: Springer; 2016. p. 285–95 .


