MAA103 Assignment Sample – Research Methods 2022
Introduction
Mobility refers to the possibility or portability of opening multiple bars in different places and using varied kinds of mobile devices. At these days the popularity of several mobile applications has been increased by the mobile technology and internet. A mobile application refers to software applications that use your mobile device. Computer system is protected by cyber security or Computer security, which is also known as IT security from damage or theft to existing software, or information, as well as services provided.
These include physical accesses’ controls to mobile hardware, along with the security for the damaged due to the access of networks data and code injections, and protection of operators from intentional, unintentional or unsafe deviations (Elgendy et al. 2019). The importance of this field is due to the reliance of many communities on computers and Internet systems, wireless networks for instances Wi-Fi, as well as Bluetooth and the development of “smart” devices, comprising televisions, smartphones, as well as smaller devices as part of the Internet of Things. The service (DOS) is designed to create machines or network resources unreachable for users who are denied access.
Attackers may deny individual hunting services, such as regularly entering incorrect passwords to lock an accident victim’s account, or they may burden the network or machine, and block all users at the same time. By adding new firewall rules, network attacks can be blocked from new IP addresses, many types of “Distributed denial of service” (DDoS) attacks are probable, so these attacks come from many points – and are more difficult to protect (Zhang et al. 2018).
Research Question
- What types of threats and security issues address in mobile computing?
- What are the solutions in regard to data security issue in cloud computing?
Systematic approach to Literature Review
Threats and security issues in mobile computing
In terms of mobile computing, three main segments are there such as Confidentiality, Integrity, and Availability (CIA). In addition, the attacks normally target either one o these segments or more than one segment or else can cause major damage to the system. The CIA can be briefly described as mentioned below:
- Confidentiality: This prevents unauthorized access to files or systems by the attacker. It works with data privacy.
- Integrity: It modifies, deletes, or deletes data on systems or files in any way.
- Availability: This ensures that data is accessible to legitimate users. Other important areas associated to mobile computing and attacks could be targeted:
- Authentication:
It must do with the system of validation and verification process. Authentication tries to ensure that users actually know that they are using certain methods and certificates requested for the system related to privacy because it helps prevent unauthorized access (Ibtihal and Hassan, 2020).
- Authorization:
It validates that the user is viewing only the data which they have the rights to access. Moreover, it must work with privacy and availability, ensuring that relevant users need to be able to access and enable data.
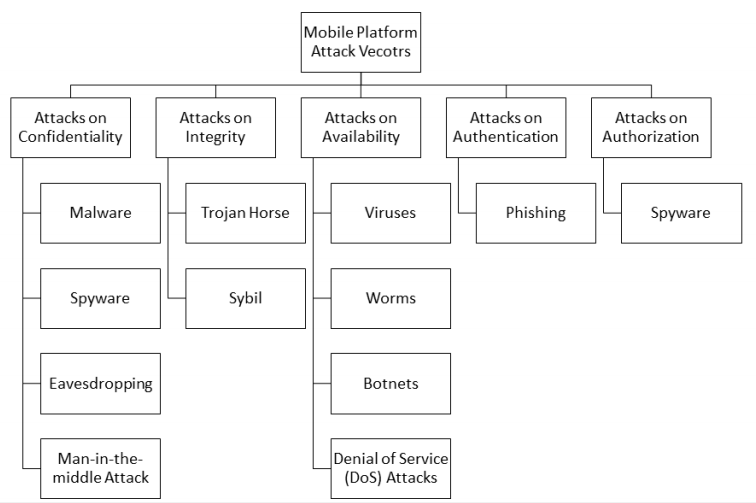
Fig 1: Taxonomy of attack vector kinds within mobile computing
Source: Sajjad et al. 2018
- Accountability:
Responsible for the action taken by the user. It is arranged in such a way that the relationship between the system and the user cannot be denied, since the user is responsible for this action, it can also be said not to deny.
The above-mentioned figure displays the taxonomy of attack vector types particularly applied to mobile computing platforms. While there is a solution to most of these attacks, the solution is also limited. In the next sections, various types of attacks on specific defensive areas can be seen. Every single attack instantly follows a solution.
Solutions in regards to data security issue in mobile computing
- Attacks on Confidentiality
Malware detection program can be applied to identify and get rid of several malware from the device, such as Trojans, worms, and viruses that will be discussed. There are different anti-virus applications in the Android in its Play store, it is suggested to install them on one of the devices. Primary detection is the most crucial aspect in minimizing the harmful impacts of malware (Sajjad et al. 2018). Through the years, several malware detection procedures have been recommended. It can be generally classified into:
- Signature-based method:
As stated by Li et al. (2018), Signature-based infiltration methods detect the signature-based malware. Firstly, it collects the data and analyze it, then the file or program with the same signature to existing malware (compared to the database) is identified. This method is often used to detect symptoms of popular malware, but it is slow because signatures have to be compared with large databases, which means they do not work quickly. Additionally, data mining methods in these applications are used to classify malware and it was very effective. In addition, it includes decision tree, Rain Forest Neural network, Naive Base, Bayesian, and “Classification-based Multiple Association Rule” (CMAR).
- Change-based method:
Change-based identification is a way to detect when changes happens within the system. It depends on probability distribution to identify the change. These methods include offline and online change detection technique.
- Anomaly-based method
The anomaly-based system detects abnormal conduct in the system considered as anomalies. This anomaly is first identified by modeling or estimating the average performance of the system. At that point, any deviations or changes from the predicted average behavior (mainly above the predetermined threshold) are identified as a potential attack.
As referred by Kumar et al. (2018), anyone can use personal firewall software to control access, although malware attack can be prohibited through installing anti-malware software in the mobile device. Because all kinds of data into and from the device go through the firewall, the system may reject access to undesirable intruders. While these solutions seem reasonable, they have two major flaws. First, this type of software uses a lot of power when installed on mobile device. Therefore, most users try to install it to save energy. Then again, the user is forced to buy a very expensive battery to reach the wanted battery life. Secondly, they restrict with website link, access to specific internet update, and other applications.
- Attacks on Integrity
The solution to Trojan horse attacks is to explain in detail how to prevent malware attacks. Various solutions are available to prevent the impact of Sybil attacks. One solution to this attack is to prevent the Sybil invaders from creating a false identity. It can be completed by implementing additional infrastructure that creates a connection between identity and cryptographic keys. In addition, some examples of such infrastructure contain public key servers and admissions control.
The weakness or problem with these solutions is that adopting this infrastructure in any network is not easy and very expensive. One more solution is to install SybilGuard that is a disclosure method for peer-to-peer users’ social media. Moreover, this process can be used by detecting Sybil that exchange keys among the users and a restricted number of their trusted friend. Through merging this social network, the observers or users can observe that the Sybil attacker has a few friends, therefore, it will be easier to detect them. Besides, the issue with SybilGuard is that it faces false negative or high misclassification. In some cases, for example, one honest user is unethically recognized as Sybil attacker (Bouazzouni et al. 2018).
- Attack on availability
Similar other malware threats, installing anti-malware can at least prevent or limit virus and worm infections on mobile phones. To overcome the Denial of Service (DoS) attack, users install a highly dedicated DOS mitigation system. This system is needed to filter out harmful traffic. Typically, they are installed ahead of the server and the router. Otherwise, any person is able to use the cloud computing mitigation provider, which is generally expert in DOS mitigation.
That way, one must be cautious when dealing with email that look to derive unrecognized sender. Moreover, one must be careful to be protected from all spam. Additionally, one must be suspicious with any email that request confirmation on their personal information or financial information. These requests are generally made in an emergency and often, they can seem when people are connected to the Internet for working, which may or may not be linked to the type of information requested by email (Huang et al. 2018).
In some situations, the mails will threaten the user with some powerful information to force it to be effective quickly. Second, one must ensure that personal information will be communicated as long as the mobile device is secure. By doing so, they should also make sure that their secure website has been used. One of the greatest ways to differentiate among insecure and secure websites is to make sure the website URL starts with “https” and not just “HTTP”. Moreover, URL that has “s” tend to be more protected because “s” stands for secure. Also, users can prevent phishing by confirming this information when receiving calls from numbers not stored on the mobile device. This should happen, especially where the user has already started the call (Mo et al. 2019).
Challenges and Limitations
As mentioned by Meng et al. (2018), various security challenges are related to mobile computing, some of which are covered in previous sections. This challenge is because of borders in mobile computing set-up and because of the absence of compliance on the user consent. In addition, absence of centralized administration in mobile network is one of the difficulties facing mobile computing security and inconsistent security standards.
Furthermore, the power of electricity limits the effectiveness and efficacy of antimalware solution in mobile device. Generally, these types of anti-malware have to be searched through a large database which makes the capabilities of these devices more undesirable than before. For users, users usually help on behalf of the other person so that the phone cannot be controlled so you can control and add more functionality.
However, it makes the device vulnerable to attack easily. One more limitation is because of human error. Regardless of every information, one tends to overlook or make errors openly and they transpire being affected by attack. Thus, it is recommended that every mobile computing user to confirm their devices are secured by spam filters, anti-virus, secure firewalls, and anti-spyware software.
In spite of these points of interest, outsourcing of information on cloud environment experiences different downsides too, for example, Data security hazard, client need to outsource their private information to untrusted server and this could group numerous security dangers to the information from server administrator and programmers.
As cloud servers give server access through http URL so web network is must for versatile clients to interface with servers. User doesn’t have physical ownership of information and there is possibly a threat on information consistency, in this way it is constantly required to keep reinforcement of information outsourced on server. Moreover, the key services are another tremendous territory of exploration and still studies are going ahead to make key administration more secured and productive (Kumar et al. 2018).
Results, Analysis and Conclusion
The qualitative method will be used by the researcher for the present study. Based on the question of this study, the researcher will perform various journal analyses to collect potential data. A much more flexible approach is provided to the researcher by qualitative data analysis method. With regard to this data collection method, researcher will be able to gain the details about the present study through collecting data from various authorized as well as reliable sources.
This study mainly outlines in regard to the types of attack in the mobile ad hoc networks. Two sorts of intense attacks are there, and these are internal attacks along with external attacks. In addition, internal attacks are dangerous for mobile ad hoc networks. Then there are brief introductions to attacks on mobile ad hoc networks, for instances, impersonation attack, denial-of-service (DoS) attack, attack against routing, and eavesdropping attack.
We analyze the basic security criteria of mobile ad hoc networks, which should be considered as guidelines for solving security issues in our mobile ad hoc ad networks. In response to these attacks, we have reviewed a number of security plans that could address security issues on mobile ad hoc networks. The concept of mobile computing has evolved over the last decade as computers have shrunk in size and computing power has increased. Computing Computers is a general term developed in modern usage to mean that mobile computing activities have to be with the Internet or on private networks and wireless.
Mobile computing security is still a threat to attackers who gain access to communication channels. These attacks may include phishing, Sybil attacks, denial of service (DOS) denial, camouflage, malware and other changes to messages. It can be prevented by using encryption such as firewalls, anti-malware software and standalone software.
Even though all of these solutions have some drawbacks, additional steps need to be taken to overcome these limitations. In my opinion, users should also be aware of security and not just apply applications to smartphone. The application should be examined before downloading and users must be aware of unwanted messages, emails, and wireless network provided. along with that, it can be stated that a number of measures are there related to network security for preventing attacks but users need to be conscious about this issue in an attempt to be secure from the evolution of the bad software world.
References
Bouazzouni, M.A., Conchon, E. and Peyrard, F., 2018. Trusted mobile computing: An overview of existing solutions. Future Generation Computer Systems, 80, pp.596-612.
Elgendy, I.A., Zhang, W., Tian, Y.C. and Li, K., 2019. Resource allocation and computation offloading with data security for mobile edge computing. Future Generation Computer Systems, 100, pp.531-541.
Huang, Q., Yue, W., He, Y. and Yang, Y., 2018. Secure identity-based data sharing and profile matching for mobile healthcare social networks in cloud computing. IEEE Access, 6, pp.36584-36594.
Ibtihal, M. and Hassan, N., 2020. Homomorphic encryption as a service for outsourced images in mobile cloud computing environment. In Cryptography: Breakthroughs in Research and Practice (pp. 316-330). IGI Global.
Kumar, P.R., Raj, P.H. and Jelciana, P., 2018. Exploring data security issues and solutions in cloud computing. Procedia Computer Science, 125, pp.691-697.
Li, J., Zhang, Y., Chen, X. and Xiang, Y., 2018. Secure attribute-based data sharing for resource-limited users in cloud computing. Computers & Security, 72, pp.1-12.
Meng, T., Wolter, K., Wu, H. and Wang, Q., 2018. A secure and cost-efficient offloading policy for Mobile Cloud Computing against timing attacks. Pervasive and Mobile Computing, 45, pp.4-18.
Mo, J., Hu, Z., Chen, H. and Shen, W., 2019. An efficient and provably secure anonymous user authentication and key agreement for mobile cloud computing. Wireless Communications and Mobile Computing, 2019.
Sajjad, M., Abbasi, A.A., Malik, A., Altamimi, A.B. and Alseadoon, I.M., 2018. Classification and mapping of adaptive security for mobile computing. IEEE Transactions on Emerging Topics in Computing.
Zhang, J., Chen, B., Zhao, Y., Cheng, X. and Hu, F., 2018. Data security and privacy-preserving in edge computing paradigm: Survey and open issues. IEEE Access, 6, pp.18209-18237.
Know more about UniqueSubmission’s other writing services:


I am currently writing a paper that is very related to your content. I read your article and I have some questions. I would like to ask you. Can you answer me? I’ll keep an eye out for your reply. 20bet