Social Impact Assessment for ICT
Executive summary
The aim of this report is to analyze the disruptive innovation and its impact on the workforce’s employment. However, the increasing trend of mobile technology gives rise to the innovation of varies application and digital payment is the one which gains high acceptance in the current business scenario. So, the payment through facial posture is the new disruptive technology that changes the payment process and supports the secured transaction. This technology supports the individuals in term to not carry the handset always on any store or assist the business to reduce customer complaints about the improper payment facilities. The types of mobile payment options such as QR code, Wallet, PoS, NFC and pay by face options are being used. Other than this payment method, there is also another mode of payment optionswhich includes SMS payment and direct carrier billing. Moreover, this technology implementation also demands the necessary ICT skills among the individuals so that the best experiences can give to the customers. However, this technology also affects the workforces of countries as with the increasing innovation in IT sector, the requirement for workers get reduced and this result in influencing their livelihood as without job, it becomes difficult to improve their standard of living. This problem is increasing rapidly in the current business environment where people struggle for their livelihood.
This report is based on evaluating the mobile payment application which has been developed to make payment for a product or a service through the help of portable electronic devices which includes smartphones and electronic devices(Jin, Wang, Qu, Guo, & Li, 2017). As the report progresses, it will also discuss the description of mobile payment along with identifying how the technology could disrupt the current way society functions. Moreover, during this report, it will also discuss the risk and opportunities that are associated with mobile payment options. The appendix b of this report will discuss ethical responsibilities that are associated with the ICT workforce. Finally, recommendations will also be provided to minimize the disruption of the technologies.
The increasing technology puts pressure on the firm to get incorporated it into the business process. The technology adaptation also demands the skilled technical staff who can manage the technology. So, the installation of advanced technology is important to sustain for a longer duration in this competitive business environment(Sessums, McHugh, & Rajkumar, 2016). However, mobile technology recently includes disruptive innovation which gives rise to strong transformation to many business sectors. This is the mobile payment through the application of pay by face and it is a secured innovative technology in which customers can make a purchase simply posing behind the point-of-sale machines equipped with cameras. These are linking an image of their face to a digital payment system or bank account. For this payment pattern, the customer or individual does not require to bring the mobile phone. So, this disruptive innovation proves to be quite beneficial in terms to solve the major problem of stolen of mobile set and access individual information from card payments. This facial recognition technology tend to achieve greater acceptance by the individuals or different companies as it reduces the burden to carry out the handset all time and for firms, it becomes easy for them to get a delay in customer services and enhance their experiences through gain high level of satisfaction(Ebersold & Glass, 2015). This technology can be adopted by the telecommunication firms, IT firms and retail sectors. These business entities majorly get a profit with the incorporation of this technology.
In order to incorporate the application face by pay, it is important for the business to have the workforces which possess ICT or necessary technical skills as these expertise people able to manage different processes for installation of application into the business(Theguardian, 2019). This technology proves to be disruptive for human resources as after the installation of this system in mobile then the requirement of large workforce gets reduced which could create the problem of unemployment. But at the same time, this application supports the security in mobile payment and reduces the chances of unauthorized access to confidential information. Therefore, it can be stated that facial payment application in mobile phones tends to be disruptive technology which changes the digital payment system.
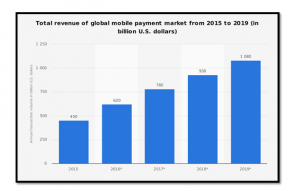
Figure 1: Total revenue of global mobile payment market from 2015 to 2019 (in billion U.S dollars); Source: (Statista, 2019)
2 a. Description of the technology
The mobile payment system is generally referred to as the payment services that are operated under financial regulation which are performed from or via a mobile devices. Mobile payment options are also used to send money to friends and family members such as with the application of PayPal and Venmo. The application of mobile payment has transformed the shopping experiences for the customers such as mobile payment options are made available on-site at stores by scanning the barcode on an app through the phone(Dahlberg, Guo, & Ondrus, 2015). The mobile payment options have made it easier for the customers to shop conveniently which provides them enriched experiences. Mobile payment options come with upgraded technologies that benefit in increasing efficiency along with providing seamless transactional activities. Mobile payment options come with a fingerprint scan or PIN input that makes the mobile payment options more secured and reliable(Cardina & Huggins, 2015).
Description
QR code payment method is determined as the contactless payment method in which the payment is made by scanning the QR code with the help of the mobile app(Green, 2014). In concern of the QR code payment technology, it is reflected that this is an alternate of the electronic funds’ transfer at the situation of point of sales by adopting the payment terminal.
Digital wallet payment system is also considered as the alternative of the electronic fund transfer at the point of the sale.Moreover, a digital wallet is also identified by the name of “E-Wallet” which is referred to as an electronic device as well as online service which give permission to an individual to conduct the electronic transactions. In respect of the wallet method, it is mentioned that it is beneficial for the users by facilitating and accelerating the checkout process(Ramos-de-Luna et al. , 2016).
While discussing the PoS, it is examined that it is the moment in which a transaction is finalized. Similarly, it is also the moment in which the payment is tendered by the customers in the exchange of the required products and services(Murdoch and Anderson, 2014). Under the point of the sales payment system, each kind of payment form can be adopted by the customers like cash, debit cards, credit cards, different mobile payments and the accumulated loyalty points too.
NFC payment system is also one of the payment methods and in concern of it, it is reflected that NFC payment is contactless payments which adopt the Near Field Communication (NFC) technology in respect to exchange the data among the readers and the payment devices such as Android Pay e-Wallets, Apple Pay, and the EMV chip cards etc. In this manner, the key aim of NFC payment is to make the payment system more futuristic(Soramäki and Cook, 2013).
Pay by face is also one of the payment methods which can be adopted by the customer while making the payment to another person. Under this technique, customers purchase the products simply by posing in front of the PoS machine which contains the cameras which work after attaching an image of the customer’s face with the digital payment system as well as a bank(Isaac and Sherali, 2014). This Pay by face technology is quite effective for those who often forget to bring their phone or cash with them and with the help of this technology, they can pay by their face.
Pros and cons of each technology
Pros:
- With the help of the QR code, the organization’s printed marketing costs can be low.
- Audiences’ responses can be tracked quite easily.
- It is used in the Smartphone.
Cons:
- It is not quite enough to provide the simplest customer experience.
- It is important for the business owner to add a reason behind using the QR code.
- It is not a two-way communication method.
Pros:
- It is more convenient for customers.
- It is quite secure as compared to other alternatives.
- Before making the payment, it requires the customer’s authorization.
- It accepts all types of cards by providing them access.
Cons:
- It is only for the limited retailers.
- For using the wallet, it is important to have a smartphone.
- While using the e-wallet, a certain amount is charged and it is compulsory to be paid.
Pros:
- It provides a good overview of the business.
- It also maintains the record of the cash flow automatically.
- PoS System also keeps the information about the business’s financial status, inventory status and sales status.
- This payment system is quite user- friendly so that the customer can use it easily.
Cons:
- This PoS system is less secured in comparison to other payment methods.
- PoS payment system has the issue of durability.
- It is more expensive for the business owner as well as users too.
Pros:
- NFC is more convenient for the customers as well as business owners.
- It makes the payment process easy for the customers.
- It is a simple payment process and easy to understand.
Cons:
- Under this system, lack of availability is one of the major issues which increases the user’s tension.
- Under this, the large amount of data is stored in the user’s electronic device automatically so there is a risk of hacking the information.
Pros:
- It is more convenient for both parties such as users and business owners.
- Under this system, there is a very low risk of stolen of payment.
- Business owners provide different offers while making the payment at the time of purchasing.
- There is no need of smartphone or cash.
Cons:
- In this system, there is a requirement of the customer’s image to link with the digital payment system or bank account.
- Hackers can hack the customer’s private information in pay by face payment system due to the lack of security.
Different types of mobile payment options that are being considered are QR code, Wallet, PoS, NFC and pay by face options.Other than this payment method there is also another mode of payment optionswhich includes SMS payment and direct carrier billing. Both of the payment options are easily available for the customers as a result of which it becomes easier for them to perform their daily tasks such as paying bills and transfer small amount of money Evidence gathered from different sources it has been noticed that acceptance of mobile payment system among people has increased by 11% due to availability of smartphones and faster internet options. With the help of advanced mode of mobile payment option, it has become easier for the customers to shop hassle-free and conveniently so that they can save their time and money and avail better opportunities.Each of the transactions made with the help of a mobile payment system generates security codes that encrypt all the transactional information and is much more secure than using a physical card(Cnet, 2019). The mobile payment system is secured with the help of digital authentication which allows the users to use their smartphone devices as their ATM card and scan them to make payments. Using smartphones for payment increases safety features because it is controlled by the authentication of the user and smartphone brand which increases its reliability among the customers. Artificial intelligence is also used for mobile payment system which uses m-POS units which are wireless devices that replicate traditional cash registers and sale terminals(Dorso & Alao, 2015). The mobile payment system is also secured with the help of two-factor authentication, this technology helps the users to secure their personal information so that the risk of data theft can be minimized. The mobile payment system also comes with automated payments, intuitive click & Brick that provides opportunities to the customers to increase their shopping experiences.
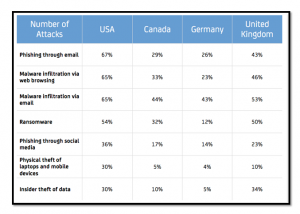
Figure 2: Increase in the number of the attacks due to the mobile payment system; Source: (Archiware, 2019)
2 b. How technology could disrupt the current way society functions
The development of the mobile payment system can disrupt the current way of social functions such as not everybody has the knowledge of using digital transactions and hence its reach is only limited to urban and semi-urban centers and therefore it becomes challenging in implementing mobile payment systems in rural areas and among illiterate people. Advancement in the mobile payment system also impacts other business organisation such as its impacts on street shopping vendors and small SMEs business. It has been noticed that most of the street shop vendors and SMEs operate in cash as a result of which it might affect their business operations(Economictimes, 2019). Cash transactions are used to purchase inventories and other resources in rural areas due to the non-availability of internet connections. Hence, if the mobile payment system fully takes over then it becomes difficult for the small SME business ventures to operate their business and achieve success. Moreover, it has also been noticed that due to the implementation of a mobile payment system it also impacts the job such as in developing countries where most of the small traders and farmers rely on cash transactions they might have to lose the job due to the mobile payment system. Furthermore, it has been noticed that due to the application of the mobile payment system it also impacts the lifestyle of the people such as due to lack of proper knowledge among the people it increases the risk of data theft(Oliveira, Thomas, Baptista, & Campos, 2016). It has been noticed that people lacking proper knowledge of operating cash related transactions through mobile applications expose their data as a result of which it increases cyber-attack and risk of data theft. Another challenge that has been noticed with the mobile payment system is that any form of digital payment such as internet banking and credit cards involves transactional fees which are not the case with cash transactions. Therefore, evaluating the fact it has been noticed that the mobile payment system might disrupt the current way of society functions.
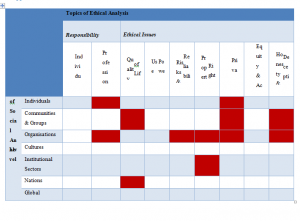
d. Identify what ethical responsibilities the existing ICT workforce has to support the integration of these technologies into businesses and daily life
Ethical responsibilities that the existing ICT workforce needs to support the integration of mobile payment system into business and daily life includes the protection of nonpublic personal information. These ethical responsibilities are maintained under section 501 of GLBA, where all the business organisation is obliged to protect the security and confidentiality of the customers. The information that is provided by the people to the business organisation is being stored and secured so that under no circumstances the information gets leaked or is used by third-party vendors for illegal activities(Selvadurai, 2013). Under section 501 of GLBA, the organisation also uses the technology to provide safety of the consumer privacy data by establishing appropriate administrative and physical safeguards. Furthermore, under the Gramm-Leach-Bliley Act (GLBA) it becomes essential for the organisation to encrypt mobile P2P payments which are secured with the help of emails and phone numbers. Therefore, the ethical responsibility that is used by the ICT workforce manages them to protect unauthorized access and anticipated threats.
c. Identify what risks and opportunities the technology provides
The risk that has been identified with the mobile payment system is that due to lack of proper transactional process, the personal information of the customers is exposed and gets vulnerable to data theft and risk of cyber-attack. The risk of cyber-attack leads to data loss and personal information of the customers which devalues customers’ trust towards mobile payment options. In developing and under-developing countries lack of proper training and information is a huge risk that might disrupt the overall functions of the mobile payment system(Taylor, 2016). Finally, the lack of proper infrastructures such as the availability of internet and capital investment could also restrict the growth of the mobile payment system. Contradictory to it the opportunities that have been identified for the mobile payment system include saving the time of the people, digital form of payment system enables the customers to make a purchase and pay through a digital platform that is easier and convenient(Slade, Williams, Dwivedi, & Piercy, 2015). Furthermore, it has also been noticed that it also helps in developing the economy such as using a mobile payment system it helps in circulating liquid money that boosts the economy and helps in reducing illegal activities. Compared to cash transactions digital form of payment are easier to carry and safe to handle as all the information are stored in smartphones and secured by two-factor authentication.
e. What recommendations could you make to minimize the disruption these technologies
The recommendations that are being provided to the organisation would help them in improving the mobile payment system along with upgrading the technologies upon which it becomes easier to minimize the threat of disruption of technologies.
The first recommendation is about securing data storage in regards to privacy information. It is encouraged by the organisation not to store any nonpublic information on mobile devices. Rather it is recommended that mobile devices need to be used to read payment information but not to store public information.
NFC chip could be used to store payment information because NFC based payment methods act similar to the contactless payment card system, which can be used to maintain security and confidentiality. Therefore storing payment information in the NFC chip is justified.
The next recommendation for the business organisation in regards to the mobile payment system includes using integrity and ethical sense in designing and implementing mobile payment applications. The information that is accessed by the organisation needs to be secured so that all the information of the customers can be stored and ethical responsibilities can be maintained within the organisation.
The different types of mobile payment options will have its own unique features such as QR code which are known as contactless payment method and the payment will be mainly made through scanning the QR code using mobile application. Moreover, this form of payment option will also use for electronic funds transfer at point of sale using a payment terminal. The risk that is associated with this application is that it increases the risk of data theft due to the attack from malware and viruses(Green, 2014). The risk that has been identified with QR code of mobile payment option includes when scanning a QR code, instead of getting the application, the data encoded with QR code send anonymous text messages that charge several cost from the customers. Furthermore, it has also been noticed that smartphone is also affected by malware, spyware and viruses that increases loss of data and crucial information for the customers.
Whereas, wallets in mobile payment system will be used as the digital wallet which will refer to the electronic devices or the online services that will allow the customers to make electronic transactions. The digital wallet will be linked with an individual’s bank account through which the users will make their payments. The risk of cyber-attack also increases such as failure to secure the data of the customers by maintaining and storing those increases risk of cyber-threat resulting loss of personal details and information. Besides the risk that has been noticed in digital wallet is that it increases the risk of cyber thieves that increases risk of networking spoofing as a result of which it increases data breach and loss of personal data.
Evaluating Near-Field Communication, it has been identified that payments will be made via using portable devices such as smartphones and credit cards that will allow the users to make payments and secure their transactional details. The security risk that has been identified with NFC technology is that while transferring data from one device to another, any third device could intercept the data as a result of which it can increase the risk of data corruption, data insertion and data modification(Coskun, Ozdenizci, & Ok, 2013). Manipulation of data also increases due to this threat as a result of which data cannot be reached to its users.
PoS in mobile payment system will enable the customers to make payment through an internet platform, point-of-sale is also paired with additional PoS hardware such as barcode scanner and cash drawer. Pay by face is an innovative mobile payment option where the people will be using their facials to make payments through facial technology. The risk that is most common with PoS mobile payment options will be that of unauthorized access to point of sale application resulting in stealing personal information and sensitive information including debit and credit card information(Crowe & Tavilla, 2012). Besides, it is also vulnerable to a malware attack in the point of sale application that exposes the personal information of customers.
Additionally, with this new payment system, people will simply pose in front of the camera, where their facial images will be linked to the bank account through which transactions are processed. Disruption in technology is one of the major risk that arise in pay by face mobile option as because the concept is currently new and as the information of the customers are directly linked with the bank, therefore if data gets loss then chances of cyber-attack will also increase and as a result of which data of customers gets loss.
SMS is one form of mobile payment option that is mostly popular among the people as it is used by people for paying for products and services via text messages(Tiwari, Sanyal, Abraham, Knapskog, & Sanyal, 2011). The customer after submitting text messages with accurate information of the payee phone number, the payment amount will be added to the mobile phone bill. The payment will be made through the phone network provider. The SMS payment method will be user-friendly, convenient and simpler, therefore, it will be famous among the people. The cons that will be associated with SMS mobile payment option is that sometimes it becomes vulnerable towards data transmission as a result of which the payment that will be supposed to process stuck due to non-functionality of payment processor. Due to the unavailability of network sometimes people will receive SMS delays as a result of which it will increase chaos among the people as they fail to complete their transactions on time.
Direct carrier billing is known is also a faster mode of mobile payment option because it is a faster way of paying bills and money through carrier instead of using bank or card details(Kent, 2012). People will access information from the app where will they upload their documents and personal details, once after few authentication steps in relation to confirm that the owner will use it the payment then is deducted from the phone bill or prepaid SIM card to SMS payments. The pro of using direct carrier billing is that it uses digital services such as Google Play and App Store that offers the options to pay by DCB. Whereas, the cons that will be associated with the direct billing option will be that of due to using single DIMOCO DCB API as a result of which it will become difficult for the customers to integrate their data and information with that of the mobile payment options. Moreover, DIMOCO will hold no contractual relationship with the user if the information of the customers gets lost or stolen. Therefore this risk can disintegrate the option of the mobile payment system.
This report was based on the mobile payment system where evaluating the technology it has been identified that it benefits the people in saving time along with increasing their experiences. Different types of mobile payment options like QR code, Wallet, PoS, NFC and pay by face options are being considered. The other mode of payment optionswhich includes SMS payment and direct carrier billing are being used other than the above-stated payment methods.Each of the transactions made with the help of a mobile payment system generates security codes that encrypt all the transactional information and is much more secure than using a physical cardAs the report progress, it has also highlighted the risk and opportunities associated with a mobile payment system such as lack of knowledge increases risk and ease of payment and data security provides opportunities. Finally, ethical responsibilities that exist with the ICT workforce to support the integration of technologies have also been mentioned in this report briefly.
Archiware. (2019). Cyber-attacks-backup-medium-maximum-security. Retrieved October 13, 2019, from https://blog.archiware.com/blog/cyber-attacks-backup-medium-maximum-security/statistik-malware-spotlight-6-2017-ohne-rahmen/
Cardina, D., & Huggins, L. ( 2015). U.S. Patent . Systems and methods for randomized mobile payment, 9(117), 210.
Cnet. (2019). How-nfc-works-and-mobile-payment. Retrieved October 14, 2019, from https://www.cnet.com/how-to/how-nfc-works-and-mobile-payments/
Coskun, V., Ozdenizci, B., & Ok, K. (2013). A survey on near field communication (NFC) technology. Wireless personal communications, 71(3), 2259-2294.
Crowe, M., & Tavilla, E. (2012). Mobile Phone Technology:“Smarter” Than We Thought. Federal Reserve Bank of Boston, 1(1), 136-149.
Dahlberg, T., Guo, J., & Ondrus, J. (2015). Electronic Commerce Research and Applications, 14(5), pp. A critical review of mobile payment research, 14(5), 265-284.
Dorso, G., & Alao, R. ( 2015). U.S. Patent . Systems and methods for fast mobile payment, 9(213), 972.
Ebersold, K., & Glass, R. (2015). Issues in Information Systems. THE IMPACT OF DISRUPTIVE TECHNOLOGY: THE INTERNET OF THINGS, 16(4), 10.
Economictimes. (2019). Going-cashless-is-it-good-for-you. Retrieved October 12, 2019, from https://economictimes.indiatimes.com/wealth/spend/going-cashless-is-it-good-for-you/articleshow/55908649.cms?from=mdr
Green. (2014). Payment systems in the healthcare industry: an experimental study of physician incentives. Journal of economic behavior & organization, 106, pp.367-378.
Isaac and Sherali. (2014). Secure mobile payment systems. IT Professional, 16(3), pp.36-43.
Jin, Y., Wang, S., Qu, Y., Guo, Q., & Li, J. (2017). In International Conference on Mechatronics and Intelligent Robotics . In Study on security of mobile payment (pp. 123-127). London: Springer, Cham.
Kent, J. (2012). Dominant mobile payment approaches and leading mobile payment solution providers: A review. Journal of Payments Strategy & Systems, 6(4), 315-324.
Murdoch and Anderson. (2014). Security protocols and evidence: Where many payment systems fail. In International Conference on Financial Cryptography and Data Security, pp. 21-32.
Oliveira, T., Thomas, M., Baptista, G., & Campos, F. (2016). Computers in Human Behavior. Mobile payment: Understanding the determinants of customer adoption and intention to recommend the technology, 61(1), 404-414.
Ramos-de-Luna et al. . (2016). Determinants of the intention to use NFC technology as a payment system: an acceptance model approach. Information Systems and e-Business Management, 14(2), pp.293-314.
Selvadurai, J. (2013). Legal And Ethical Responsibilities In Mobile Payment Privacy, 5(1), 10.
Sessums, L., McHugh, S., & Rajkumar, R. (2016). Jama. Medicare’s vision for advanced primary care: new directions for care delivery and payment, 315(24), 2665-2666.
Slade, E., Williams, M., Dwivedi, Y., & Piercy, N. (2015). Exploring consumer adoption of proximity mobile payments. Journal of Strategic Marketing, 23(3), 209-223.
Soramäki and Cook. (2013). SinkRank: An algorithm for identifying systemically important banks in payment systems. Economics: The Open-Access, Open-Assessment E-Journal, 7(2013-28), pp.1-27.
Statista. (2019). Mobile-payment-transaction-volume-forecast. Retrieved October 13, 2019, from https://www.statista.com/statistics/226530/mobile-payment-transaction-volume-forecast/
Taylor, E. (2016). Mobile payment technologies in retail: a review of potential benefits and risks. International Journal of Retail & Distribution Management, 44(2), 159-177.
Theguardian. (2019). Smile-to-pay-chinese-shoppers-turn-to-facial-payment-technology. Retrieved October 13, 2019, from https://www.theguardian.com/world/2019/sep/04/smile-to-pay-chinese-shoppers-turn-to-facial-payment-technology
Tiwari, A., Sanyal, S., Abraham, A., Knapskog, S., & Sanyal, S. (2011). A multi-factor security protocol for wireless payment-secure web authentication using mobile devices. arXiv preprint arXiv:1111, 3010(1), 1.
| Social opportunity and risk categorisation | ||||||
| More buying of the smartphones and access to digital platforms for wiring of money | More people are inclined towards the digital platforms | risk of cyber-attack leads to data loss and personal
information of the customers which devalues customers’ trust towards mobile payment options. |
digital form of payment are easier to carry and safe to
handle , thus encouraging the masses to use mobile payment system. |
|||
| lack of proper infrastructures such as the availability of internet and capital
investment could also restrict the growth of the mobile payment system and thus affecting the application of the mobile payment system by the masses |
||||||
| Less likely to go to banks | ||||||
| LOW Opportunity / Impact / Consequence | HIGH | |||||
| Incidental | Minor | Significant | Major | Severe | ||
| Local, small-scale, easily reversible change on social characteristics or values of the communities of interest or communities can easily adapt or cope with change.
Local small-scale opportunities emanating from the technology that the community can readily pursue and capitalise on |
Short-term recoverable changes to social characteristics and values of the communities of interest or community has substantial capacity to adapt and cope with change.
Short-term opportunities emanating from the technology. |
Medium-term recoverable changes to social characteristics and values of the communities of interest or community has some capacity to adapt and cope with change.
Medium-term opportunities emanating from the technology. |
Long-term recoverable changes to social characteristics and values of the communities of interest or community has limited capacity to adapt and cope with change.
Long-term opportunities emanating from the technology |
Irreversible changes to social characteristics and values of the communities of interest or community has no capacity to adapt and cope with change. | ||
URLs
https://www.statista.com/statistics/226530/mobile-payment-transaction-volume-forecast/
https://www.cnet.com/how-to/how-nfc-works-and-mobile-payments/
https://sci-hub.tw/https://www.sciencedirect.com/science/article/pii/S0048733318301537
https://sci-hub.tw/https://www.sciencedirect.com/science/article/pii/S2352146517303885
https://sci-hub.tw/https://www.sciencedirect.com/science/article/pii/S1877042812052032
https://sci-hub.tw/https://www.sciencedirect.com/science/article/pii/S1877042816304712
https://sci-hub.tw/https://www.sciencedirect.com/science/article/abs/pii/S0963868707000480
https://sci-hub.tw/https://www.sciencedirect.com/science/article/abs/pii/S0969476515301636
https://sci-hub.tw/https://www.sciencedirect.com/science/article/pii/S187705091503166X
https://sci-hub.tw/https://www.sciencedirect.com/science/article/pii/S1877050916301879
https://sci-hub.tw/https://www.sciencedirect.com/science/article/abs/pii/S0969476513701450
https://sci-hub.tw/https://www.sciencedirect.com/science/article/pii/S180920391630033X



Wow, this blogger is seriously impressive!
I appreciate your creativity and the effort you put into every post. Keep up the great work!