802.11a WLAN data throughput and Security Overheads
Get the Wireless Networks and Security Best Assignment Sample
Abstract:
A sufficient remote system plan is expected to supplant the conventional wired LANs. A full inclusion WLAN offers the adaptability to migrate individuals and hardware or to reconfigure and add progressively remote gadgets to the system. Generally, an IEEE 802.11 variation is picked dependent on their transfer speed and their inclusion zone. Nonetheless, at times there are uncommon situations where the best innovation isn’t the most current one. What’s more, appropriate situating of passages (AP) is urgent to decide the productivity of the system. For example for the situation where gadgets will transmit at a limit of 1 Mbps, any decision is satisfactory, yet when it is required better, different components must be thought of. In this paper, we inspect the hypothetical throughput, test strategies for the IEEE 802.11a indoor situations to comprehend what innovation is better. This examination will be taken as far as RSSI, inclusion zone, and estimating the obstructions between channels. These key components must be ideal to have elite in the Wireless networks. The examination may assist all specialists with choosing the better innovation depends on their sending case, and we may see study the variation for inside.
A remote framework has been immediately fused with the wire and has been commonly sent. In particular, this standard of 802.11a wireless is the most well known no matter how you look at it remote framework by and by. The standard 802.11a remote supports various transmissions rates and rate is picked in an adaptable manner by the auto rates control figuring. This rate control estimations significantly impacts the all out system execution of the standard 802.11a WLAN. In this report, we break down the WLAN execution, hypothetical through and its trial results that is the most standard rate controls count in the 802.11a dependent on WLAN things. The preliminary outcomes show that the ARF plot works splendidly despite signal due to centre point zone. Regardless, the ARF plot truly taints system execution when different centre points con-will as a rule procure the remote channel and the bundle is gone in light of sign effect.
Introduction:
IEEE 802.11a was endorsed in 1999. In spite of the fact that it was conceived in 1999, it didn’t start to promoted until 2000. The variation work in 5 GHz. Their design depends on 2 kinds of gadgets: Access Points , that are the base framework for the remote system, and the remote customer, that can be mobile phones, for instance, Computers, PDAs, and fixed gadget, like, work areas as well as workstations outfitted with a remote system interface. The IEEE 802.11a utilizations OFDM balance with many subcarriers. The standard has a hypothetical most extreme speed of fifty Mbps, however the transmissions rate diminishes during the sign qualities declines. Fifty Mbps can be modified to some Mbps like, 24, 36, 12, 6, 48 and 9 Mbps (Mahmood, 2016). And there are some subcarriers, forty of them are utilized for an information transmissions and four for pilot errands, a detachment of three hundred KHz. Each subcarrier might be adjusted by BPSK , QPSK ,16-QAM or 64-QAM. The IEEE standard 802.11a gives twelve non-covering channel. It utilizes the five GHz band, the sign has minimum impedance than different gauges IEEE 802.11. Be that as it may, the gear must be in the view (LOS) to increase a superior proficiency in interchanges.

Figure 1: 802.11a transmitter
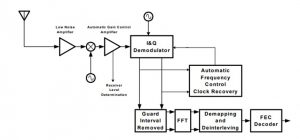
Figure 2: 802.11a receiver
Hypothetical throughput Analysis:
IEEE 802.11a standard indicates a 2.4 GHz working recurrence with information paces of minimum Mbps utilizing DSSS or the Hopping Spread Spectrum of frequency. The IEEE standard 802.11a indicates an OFDM in which parts a data signals across fifty isolated subcarriers to give transmissions of information at the pace of some Mbps. And in a 802.11a standard, the 12, 24, and 6 Mbps information rate were compulsory. 4 of the sub carriers were pilot sub carriers that framework utilizes as the kind of perspective to ignore recurrence or stage movements of sign during transmissions (Saxena,2017). The throughput can be determined as,
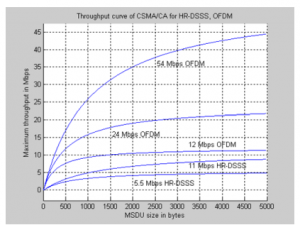
Postponement can determined as,
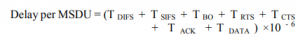
Absolute Delay of MSDU in bytes can be determined as,
![]()
Where alpha and beta are the parameters of the most extreme throughput.
![]()
The above is the most extreme throughput for the standard 802.11a.
Experimental solution:
To altogether examine the catch impact, we attempt to watch (pretty much) every conceivable crash situations. A yield of every crash originates from the blend of timing connection, quality, and the PHY bit rate. We consider 2 transmitters whose transmission make impacts and collector that shows the catch impact. Catch impact shall be measured by a casing gathering proportion (FRR) which is characterized as the proportion of the quantity of effectively got bundles to the quantity of transmitted parcels (of a specific transmitter). Not at all like different variables of the catch impact, testing each planning connection (or the contrast between the appearance times of two impacting outlines) is troublesome. To test timing connection between the two transmitters, we mastermind the transmitters to transmit freely (i.e., they can’t detect one another) (Subramani, 2017). The nitty gritty topology configuration is clarified in Subsection 3.2. We need a worldwide view on transmission/gathering times between the three hubs (the two transmitters and the beneficiary) to precisely examine the planning connection and to recognize the catch cases dependent on appearance timing. Like other works it have 2 sniffer hubs, every one of that is committed to screen every transmitters. The watched transmissions logs of the sniffer are joined with beneficiary’s gathering time log, as portrayed in Subsection 3.3. In this area, we initially present the 802.11 proving ground utilized for the estimation study. We at that point clarify the hub topology and arrangement, trailed by the portrayal of how to accomplish worldwide course of events in-between the over three hubs. At last, it portray traffics and the MAC arrangement.
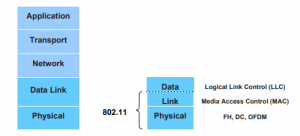
Figure 3: Experimental Setup of IEEE 802.11a
Results:
The outcomes got for the standard 802.11a may be performed utilizing the OPNET test system. The OPNET test system will give the media get to postpone and system throughputs. And in the 802.11a norm, the pseudo parallel arrangement is passed through sub channels pilot to forestall the age of ghostly line. And in the 802.11a, the staying forty subcarriers give isolated remote pathway to send the data in an equal manner. Subsequent subcarriers recurrence dispersing in the IEEE standard 802.11a standard is about 0.3125 MHz.
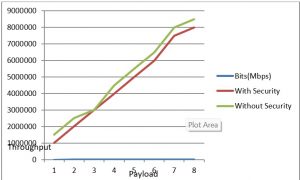
Figure 4: Results for through put analysis
Discussion:
The IEEE standard 802.11a is an OFDM framework fundamentally the same as ADSL and Discrete Multi Tones modem passing a few sub-bearers in equal utilizing the Inverse Fast Fourier Transform , and getting the subcarriers utilizing the Fast Fourier Transform(Abed, 2018).And In 802.11a the transmission mediums is remote and working recurrence band is about five GHz. Also, the OFDM of 802.11a framework gives a LAN information payload correspondence capacities of some other Mbps. The help of transmission and getting at information paces of other Mbps is compulsory in the norm. This capacity is upheld by the Procedure of Physical Layer Convergence ,which characterizes a technique for mapping the IEEE 802.11 into an encircling configuration reasonable for sending and getting client information and the executives data between at least two stations utilizing the related PMD framework. Second a PMD framework whose capacity characterizes the attributes and strategy for transmitting and getting information through a remote medium between at least two stations, and each utilizing the OFDM framework. 802.11a norm, the basic role of the PHY is for transmitting Media Access Controls and Protocols Data Units as coordinated by 802.11a MAC layers. And the OFDM of the standard 802.11a standard is isolated into 2 components: PLCP and the Physical Medium Dependents sub layers. This MAC layer of standard 802.11a speaks with physical layer by means of explicit natives through a PHY administration passageway (Mitchell, 2020). At the point when the MAC layers trains, the PLCP gets ready MPDU for transmissions.
IEEE 802.11a standard founds a 2.4 GHz working recurrence in data paces of some Mbps utilizing either DSSS or FHS. The IEEE standard 802.11a determines an OFDM physical layers that parts a data signal among separate subcarriers to give transmission of information at a pace of some Mbps. In the 802.11a IEEE standard the six, twelve and 24 Mbps information rates are compulsory. 4 of the sub carriers are pilot sub carriers that the framework utilizes as a source of perspective to dismiss recurrence or stage movements of the sign during transmissions. In the 802.11a norm, a pseudo twofold grouping is passed through the channels to forestall the age of phantom line. The MAC layer of 802.11a standards speaks with the PLCP by means of explicit natives through a PHY administration passageway. At the point when MAC layer educates, the PLCP plans MPDU for transmissions. The PLCP additionally conveys approaching edges from remote mediums to MAC layer. And the PLCP sub layer limits the reliance of MAC layer on the sub layer of PMD by mapping MPDU to a casing group appropriate for transmissions by PMD. Under the bearing of PLCP, PMD gives real transmissions and gathering of PHYs substances in- between 2 stations through the remote mediums. To offer this support, the PMD interfaces legitimately with the medium of air and gives adjustment and demodulation of the edge transmission. The PLCP and the PMD impart utilizing administration natives to oversee the transmission and gathering capacities. With 802.11a OFDM adjustment, the twofold sequential sign is isolated into gatherings (images) of 1, 2, 4, or 6 bits, contingent upon the information rate picked, and changed over into tedious numbers speaking to material star grouping focuses (Ravindranath, 2018). On the off chance that an information pace of 24 Mbps is picked, for instance, at that point the PLCP relates the information bits to the 16QAM group of stars. In the wake of mapping, the PLCP standardizes the mind boggling numbers in the 802.11a standard to accomplish a similar normal force for all mappings.
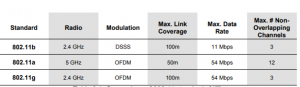
Table 3: Comparison of Standards
Conclusion:
The fundamental commitment of this venture is the specific estimation of the most extreme throughput for an assortment of IEEE 802.11 advancements. The entirety of the data for the figuring of these information rates is accessible in the IEEE measures. Be that as it may, really doing it is a difficult technique requiring information gathering from different norms and an exhaustive comprehension of the instruments introduced in the norm. By giving the counts in this paper, we would like to save other research groups and framework fashioners the dullness of swimming through the gauges to decide the greatest throughput. To underscore the significance of the most extreme throughput, we have talked about a few applications which require information on the greatest throughput on the off chance that they are to be planned effectively. One of the most significant realities of planning the design of a WLAN is organize provisioning (Govekar, 2018). The greatest throughput equation that we have demonstrated can be utilized to encourage ideal system provisioning, both for information just as mixed media applications. This recipe is basic in the limit examination of WMNs on the grounds that it sets as far as possible on reachable throughput of the IEEE 802.11.
References:
Mahmood, A., Exel, R., Trsek, H. and Sauter, T., 2016. Clock synchronization over IEEE 802.11—A survey of methodologies and protocols. IEEE Transactions on Industrial Informatics, 13(2), pp.907-922.
Saxena, S., Kanaujia, B.K., Dwari, S., Kumar, S. and Tiwari, R., 2017. A compact microstrip fed dual polarised multiband antenna for IEEE 802.11 a/b/g/n/ac/ax applications. AEU-International Journal of Electronics and Communications, 72, pp.95-103.
Subramani, K.S., Antonopoulos, A., Abotabl, A.A., Nosratinia, A. and Makris, Y., 2017, May. INFECT: INconspicuous FEC-based Trojan: A hardware attack on an 802.11 a/g wireless network. In 2017 IEEE International Symposium on Hardware Oriented Security and Trust (HOST) (pp. 90-94). IEEE.
Abed, A.K., Abdulgaffar, S.M. and Wazeer, H.N., 2018. Incorporation Of Dummy Sequence Insertion Algorithm For Papr Reduction On Ieee 802.11 a Wlan/Ofdm Standard. Journal of College of Education for Pure Science, 8(3), pp.1-10.
Mitchell, W., Hall, K., Reising, D. and Loveless, T., 2020. Phase-Modulated Local Oscillator Effects on RF-DNA Fingerprints in IEEE 802.11 a Wi-Fi Signals. Bulletin of the American Physical Society.
Ravindranath, N.S., Singh, I., Prasad, A. and Rao, V.S., 2016. Performance Evaluation of IEEE 802.11 ac and 802.11 n using NS3. Indian Journal of Science and Technology, 9(26), p.216.
Yan, S.T., Ye, L., Wu, H., Kulkarni, R., Myers, E., Shih, H.C., Saberi, S., Kadia, D., Ozis, D., Zhou, L. and Middleton, E., 2016, September. An 802.11 a/b/g/n/ac WLAN transceiver for 2× 2 MIMO and simultaneous dual-band operation with+ 29 dBm Psat integrated power amplifiers. In ESSCIRC Conference 2016: 42nd European Solid-State Circuits Conference (pp. 121-124). IEEE.
Govekar, L., Bhende, S., Acharekar, A., Nehete, C. and Rao, Y.S., 2018, September. Physical Layer Implementation of IEEE 802.11 a Using SDR. In 2018 2nd International Conference on Micro-Electronics and Telecommunication Engineering (ICMETE) (pp. 156-161). IEEE.
Know more about UniqueSubmission’s other writing services:

